Secure & Compliant Cloud Environments
Strengthen your cloud security posture with compliance-driven architecture optimization, data residency solutions, and incident response planning.

Cloud Architecture Optimization & Hardening
Cross-Border Data Transfer and Cloud Compliance Advisory
Cloud Incident Response & Resilience Planning
Introduction
As businesses shift to the cloud, securing digital assets while complying with MENA’s evolving cloud regulations is a critical challenge. CloudCrest Security specializes in advising organizations on securing cloud environments, ensuring regulatory compliance, and mitigating cybersecurity risks.
Our Cloud Security Advisory Services help businesses align with:
UAE Information Assurance Regulation (IAR)
KSA NCA Cloud Cybersecurity Controls
Qatar NCSA Cyber Assurance
Oman ITA Cybersecurity Framework
Cross-border compliance with GDPR, ISO 27001, and more
Stay Up to Date
Cloud security regulations are constantly evolving. Check our Insights for the latest updates on MENA cloud security and compliance developments.

Cloud Architecture Optimization
To assess and enhance cloud security architecture, ensuring compliance with regional cloud regulations and global security standards.
How it Works
1
Cloud Infrastructure Assessment
▪︎ Review existing public, private, and hybrid cloud environments for security weaknesses.
▪︎ Identify compliance gaps with MENA regulatory requirements.
2
Security Hardening & Best Practices:
▪︎ Implement encryption (at rest & in transit), multi-factor authentication (MFA), and IAM solutions.
▪︎ Strengthen network segmentation, logging, and threat detection capabilities.
3
Compliance Alignment:
Ensure cloud security architecture aligns with UAE IAR, KSA NCA, PDPL requirements, and more.
4
Deliverables
- Comprehensive cloud security assessment report
- Cloud security optimization roadmap
- Security hardening implementation plan
Stay Up to Date
Stay ahead of evolving cloud security risks & regulatory changes in the MENA region.
Cross-Border Data Transfer and Cloud Compliance Advisory
To help businesses meet data residency laws and ensure compliant cross-border data transfers while maintaining operational flexibility.
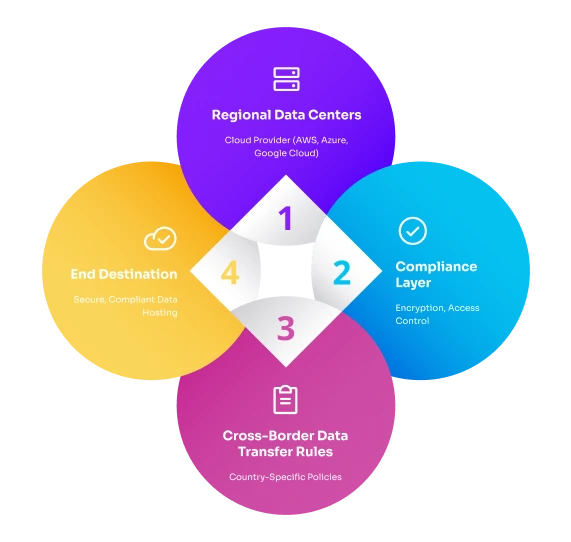
How it Works
1
Data Residency Assessment:
▪︎ Identify data localization requirements in UAE, Saudi Arabia, Qatar, Kuwait, and other MENA jurisdictions.
▪︎ Evaluate data storage, access, and transfer compliance across multiple cloud environments.
2
Data Segmentation & Sovereignty Strategies:
▪︎ Design data localization strategies for regulated industries.
▪︎ Advise on sovereign cloud solutions where mandated by law.
3
Cross-Border Data Transfer Solutions:
▪︎ Develop secure, compliant frameworks for transferring sensitive data between regions.
▪︎ Align strategies with GDPR, ISO 27001, and other global standards.
4
Deliverables
- Data residency compliance assessment
- Cross-border data transfer risk analysis
- Policy framework for cloud data governance
Stay Up to Date
Read the latest analysis on data residency trends and cloud compliance shifts in MENA.

Cloud Incident Response & Resilience Planning
To help businesses develop cloud-focused incident response strategies, ensuring a rapid, compliant response to security breaches.
How it Works
1
Cloud-Specific Incident Response Plan (IRP):
▪︎ Develop a tailored incident response framework for cloud environments.
▪︎ Ensure compliance with MENA breach notification laws (e.g., DESC ISR, Kuwait NCSC).
2
Threat & Risk Simulation:
▪︎ Conduct tabletop exercises and real-world attack simulations for cloud incidents.
▪︎ Improve incident detection, containment, and recovery procedures.
3
Automated Incident Detection & Compliance Reporting:
▪︎ Advise on SIEM integration for real-time threat intelligence & response.
▪︎ Establish structured breach reporting protocols for regulatory authorities.
4
Deliverables
- Cloud incident response strategy & playbook
- Threat simulation & response readiness assessment
- Automated compliance reporting framework
Stay Up to Date
Stay informed on emerging cloud security threats and best practices for cloud incident response.
Why Choose CloudCrest Security for Cloud Security Advisory?
Deep expertise in MENA cloud compliance & security frameworks
Strategic advisory for businesses operating in regulated sectors
Practical, hands-on security guidance for cloud infrastructure protection
Seamless integration of compliance with cybersecurity best practices